
ByBit Hack Reveals North Koreas Crypto Threat
North Korean Hackers Convert $300m from ByBit Heist Amid Global Crackdown
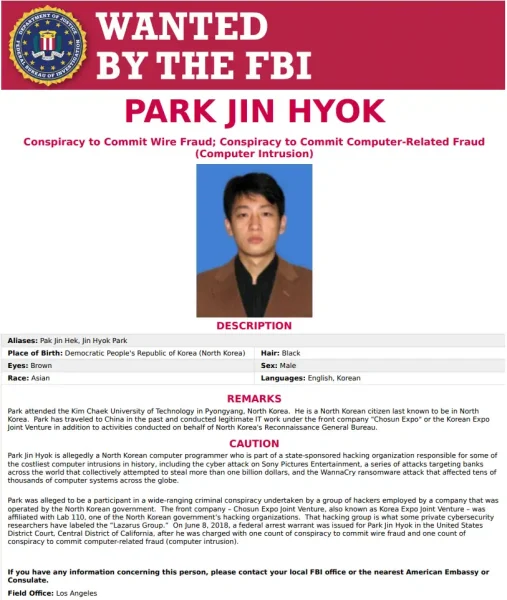
In a brazen cyber assault, hackers linked to North Korea’s Lazarus Group have laundered at least $300m (£232m) from a staggering $1.5bn cryptocurrency theft targeting Singapore-based exchange ByBit. The incident, which unfolded over two weeks ago, has escalated into a high-stakes global chase, with experts warning that the stolen funds could fuel Pyongyang’s controversial weapons programmes. Meanwhile, ByBit’s CEO Ben Zhou has vowed to “wage war” on the hackers, even as analysts highlight the near-impossible odds of recovering the majority of the pilfered assets.
The Lazarus Group’s Relentless Crypto Laundering Machine
Authorities and blockchain analysts trace the heist to 21 February, when Lazarus operatives infiltrated a ByBit supplier’s systems. By altering a digital wallet address mid-transaction, they diverted 401,000 Ethereum tokens—worth approximately $1.5bn at the time—to their own coffers. Almost immediately, the group began scrambling to convert the crypto into untraceable cash, leveraging a mix of automated tools and round-the-clock manpower.
Dr Tom Robinson, co-founder of blockchain analytics firm Elliptic, notes that Lazarus operates with military precision. “They work in shifts, pausing only for a few hours daily,” he explains. “Their expertise isn’t just technical—it’s logistical. They’ve built an entire industry around laundering stolen crypto, and they’re alarmingly efficient.” Elliptic’s data reveals that 20% of the stolen funds have already vanished into opaque networks, likely beyond recovery.
This efficiency stems from years of refinement. Since 2017, when Lazarus shifted focus from bank raids to crypto exchanges, North Korea has reportedly amassed over $3bn through cyberattacks, according to a 2023 United Nations report. The ByBit breach now ranks among their largest successes, eclipsing even the $600m Ronin Bridge attack in 2022.
ByBit’s Counterattack: Bounties, Blockades, and Borrowed Funds
Within hours of the breach, ByBit launched its “Lazarus Bounty” programme, offering rewards to individuals who help trace and freeze stolen assets. So far, 20 participants have claimed $4m for identifying $40m in waylaid funds. “Every tip matters,” Zhou said in a 27 February press briefing. “We’re collaborating with exchanges, blockchain analysts, and law enforcement to disrupt their operations.”
To reassure customers, ByBit injected $1.5bn—borrowed from investors—into user accounts, ensuring no losses for clients. Yet this move has drawn scrutiny. Critics argue that relying on debt to cover heists sets a risky precedent, particularly as Lazarus continues to exploit weaker links in the crypto ecosystem.
One such weak link is eXch, a Malta-based exchange accused of processing over $90m of the stolen Ethereum. Johann Roberts, eXch’s founder, initially refused to freeze transactions, citing a “lack of conclusive evidence” and a bitter feud with ByBit over past business disputes. After mounting pressure, Roberts claims to now be co-operating but remains defiant. “Crypto’s promise is anonymity,” he wrote in a 1 March email. “If we police every transaction, we betray that principle.”
Global Reckoning: Sanctions, Sanctions, and Stalemates
The ByBit hack has reignited debates about regulating decentralised finance. Unlike traditional banks, crypto exchanges often lack robust identity checks or transaction reversal mechanisms, making them prime targets. The US Treasury’s 2022 sanctioning of Tornado Cash—a crypto-mixing service used by Lazarus—highlighted efforts to curb such crimes. Still, enforcement remains patchy, particularly in jurisdictions with lax oversight.
South Korea’s National Intelligence Service estimates that North Korea ploughed 50% of its stolen crypto into missile development in 2023 alone. This figure aligns with UN findings that Pyongyang’s weapons programmes rely heavily on cybercrime revenue. Despite international sanctions, the regime’s isolation insulates it from diplomatic blowback, enabling Lazarus to operate with near impunity.
A History of High-Profile Heists
Lazarus’s track record underscores its adaptability. In 2019, the group siphoned $41m from South Korea’s UpBit exchange, followed by a $275m raid on KuCoin in 2020. While KuCoin recovered 84% of its losses through blockchain tracing, most attacks end less favourably. The 2023 Atomic Wallet breach, which netted $100m, saw nearly all funds vanish within days.
Analysts attribute this success to North Korea’s unique position as a state-sponsored hacking entity. “They don’t fear reputational damage or extradition,” says Dr Dorit Dor of Check Point Software. “For them, cybercrime is a revenue stream, not a rogue activity.”
The Laundering Labyrinth: How Lazarus Evades Detection
To bypass detection, the Lazarus Group employs a multi-layered strategy, blending cutting-edge technology with decades of institutional knowledge. Initially, they funnel stolen crypto through mixers—services that jumble transactions to obscure their origins. For example, Tornado Cash, a popular Ethereum mixer sanctioned by the US Treasury in August 2022, processed an estimated $455m in crypto tied to North Korean hacks before its shutdown. Despite sanctions, Lazarus pivoted to alternatives like Sinbad, another mixer later sanctioned in November 2023 after handling $100m of the ByBit heist funds.
In parallel, the hackers use cross-chain swaps, converting Ethereum into privacy-focused coins like Monero, which conceal transaction details by default. Chainalysis, a blockchain forensics firm, estimates that 40% of funds stolen in 2023 crypto heists were converted into Monero within 72 hours. This tactic complicates tracking, as Monero’s blockchain lacks the transparency of Bitcoin or Ethereum.
Adding another layer, Lazarus often routes funds through decentralised exchanges (DEXs), which don’t require user identification. A 2024 report by Elliptic found that DEXs facilitated $900m in illicit crypto transactions last year, with Lazarus accounting for nearly a third. Once “cleaned,” the crypto moves to mainstream exchanges in jurisdictions with lax regulations, such as Seychelles-based platforms, where it is cashed out into fiat currency.
Global Responses: Sanctions and Cyber Diplomacy
Governments and regulators, however, are scrambling to close loopholes. In March 2024, the US Office of Foreign Assets Control (OFAC) sanctioned three Seychelles-based exchanges linked to laundering $200m from the ByBit hack. Similarly, South Korea’s Financial Intelligence Unit froze $12m in assets tied to Lazarus-operated shell companies. These measures, while impactful, face limitations. “Sanctions only work if everyone enforces them,” says Laura Greaves, a senior analyst at Silverado Policy Accelerator. “Many offshore platforms simply ignore compliance.”
Meanwhile, international coalitions like the UN’s Cybercrime Treaty negotiations aim to standardise crypto regulations. Progress remains slow, though. At a February 2024 Interpol summit, only 37 of 195 member states agreed to share real-time data on crypto crimes. Critics argue that without binding agreements, such initiatives lack teeth.
Private-sector collaboration offers more promise. ByBit’s partnership with TRM Labs, a blockchain intelligence firm, has enabled the freezing of $60m in stolen funds since late February. Still, gaps persist. Johann Roberts’ eXch, for instance, continues operating despite allegations of non-compliance. “Exchanges that resist co-operation must face consequences,” asserts ByBit’s Zhou. “Otherwise, they become safe havens for criminals.”

Case Study: The $600m Ronin Bridge Attack
The 2022 Ronin Bridge attack, another Lazarus operation, underscores the challenges of recovering stolen crypto. In March of that year, hackers exploited a vulnerability in the Ronin network—a blockchain bridge linking Ethereum and the Axie Infinity game—to steal 173,600 Ethereum and $25m in USDC stablecoins. Despite swift action by Sky Mavis, Axie’s parent company, only $34m was recovered.
Key to Lazarus’s success was their use of sleeping addresses—dormant wallets that held the stolen funds for months before gradual liquidation. By the time investigators identified the wallets, 80% of the crypto had already been laundered. Sky Mavis CEO Trung Nguyen admits the breach “exposed flaws in cross-chain security,” prompting a $150m overhaul of the Ronin network.
The attack also highlighted North Korea’s evolving tactics. Unlike the ByBit heist, which relied on phishing a third-party vendor, the Ronin breach involved social engineering. Posing as recruiters, Lazarus members tricked a senior engineer into applying for a fake job, stealing credentials through a malware-infected PDF. Such methods reveal the group’s adaptability, blending technical prowess with psychological manipulation.
The Human Cost: Beyond Financial Losses
While headlines focus on astronomical theft figures, the human impact of these hacks is profound. After the Ronin attack, Axie Infinity slashed its 800-strong workforce by 30%, citing financial strain. Similarly, Atomic Wallet’s 2023 breach left 5.5 million users vulnerable to identity theft, with phishing scams surging 200% in its aftermath, according to cybersecurity firm Kaspersky.
For North Koreans, the repercussions are direr. A 2023 UN Panel of Experts report found that 70% of Lazarus’s stolen crypto funds finance ballistic missile tests, which have escalated regional tensions. South Korea’s Defence Ministry estimates that Pyongyang conducted 35 missile launches in 2023 alone, many powered by crypto-derived revenue.
Civilians also bear the brunt. “Sanctions aimed at curbing weapons programmes often exacerbate humanitarian crises,” notes Dr. Kee Park, a Harvard Medical School lecturer who works on DPRK health projects. “The regime prioritises military spending over food imports, leaving millions malnourished.” In 2023, the World Food Programme reported that 42% of North Korea’s population faces food insecurity—a figure compounded by the regime’s diversion of resources.
Technological Arms Race: Can Crypto Ever Be Secure?
In response to escalating threats, blockchain developers are racing to fortify systems. Innovations like zero-knowledge proofs—a cryptographic method that validates transactions without revealing sensitive data—aim to enhance privacy without aiding criminals. Ethereum’s upcoming “Prague” upgrade, slated for late 2024, will integrate these proofs to deter address spoofing.
Simultaneously, AI-driven monitoring tools are gaining traction. London-based startup CryptoGuard uses machine learning to flag suspicious wallet patterns in real time, claiming a 95% accuracy rate in identifying Lazarus-linked transactions during the ByBit heist. Still, sceptics warn that hackers could weaponise AI themselves. “It’s an arms race,” says CryptoGuard CEO Amira Patel. “For every defence we build, Lazarus develops a countermeasure within weeks.”
Regulatory pressure is also mounting. The EU’s Markets in Crypto-Assets (MiCA) framework, set for full implementation in December 2024, mandates stringent identity checks for transactions over €1,000. While laudable, experts like Dr. Robinson argue that “regulation alone won’t suffice. The industry must adopt proactive security practices, not just compliance checklists.”
A Glimmer of Hope: The Role of White-Hat Hackers
Amid the gloom, white-hat hackers and ethical collectives are emerging as critical allies. Blockchain sleuths like @ZachXBT, a pseudonymous investigator, have traced $160m in Lazarus funds since 2021, often sharing findings gratis. “These groups operate on goodwill and caffeine,” says @ZachXBT via encrypted chat. “We’re up against state-sponsored teams, but public blockchains let us crowdsource intelligence.”
ByBit’s bounty programme exemplifies this collaborative ethos. In one case, a 24-year-old developer in Mumbai identified $8m in stolen Ethereum by analysing transaction timestamps and gas fees—a feat that earned him a $800,000 reward. “I didn’t expect to succeed,” he admits. “But seeing Lazarus’s patterns gave me a roadmap.”
Despite such victories, the odds remain steep. For every frozen wallet, Lazarus creates ten more, often pre-loaded with decoy transactions to mislead trackers. “They’re masters of distraction,” says @ZachXBT. “One slip-up, and the trail goes cold.”
The FBI’s TraderTraitor Alert: A New Front in the Cyber War
On 11 March 2025, the FBI issued a public service announcement labelling North Korea’s cyber operations against ByBit as “TraderTraitor,” urging global crypto firms to block transactions linked to 38 Ethereum addresses tied to the heist. Among these, wallets like 0x51E9d833Ecae4E8D9D8Be17300AEE6D3398C135D and 0x96244D83DC15d36847C35209bBDc5bdDE9bEc3D8 held over $200m in stolen assets at the time of the alert. The bureau emphasised that Lazarus had already converted a portion of the funds into Bitcoin and other cryptocurrencies, dispersing them across thousands of addresses to evade detection.
Despite the FBI’s call for collaboration, compliance remains uneven. While major exchanges like Coinbase and Binance swiftly froze suspicious transactions, smaller platforms in loosely regulated regions hesitated. “We’re dealing with a hydra,” says FBI Cyber Division Assistant Director Bryan Vorndran. “Cut off one wallet, and three more emerge.” The alert marks a strategic shift, focusing not just on recovery but on disrupting Lazarus’s operational infrastructure, including blockchain nodes and decentralised finance (DeFi) protocols.
eXch and the Ethics of Crypto Anonymity
The role of Malta-based exchange eXch in processing $90m of the stolen funds has intensified debates about crypto’s foundational principles. Johann Roberts, eXch’s founder, initially dismissed ByBit’s allegations, citing a “lack of irrefutable proof” and framing the dispute as a clash between privacy advocates and surveillance proponents. “If we start freezing wallets on hearsay,” Roberts argued in a 5 March blog post, “we abandon crypto’s promise of financial sovereignty.”
Critics counter that such stances enable criminal enterprises. ByBit’s Zhou notes that eXch’s delayed cooperation allowed Lazarus to offload at least $30m before wallets were frozen. The standoff underscores a broader industry rift: a 2024 survey by CryptoCompare found that 62% of decentralised exchanges prioritise anonymity over compliance, compared to 18% of centralised platforms. For regulators, this dichotomy poses a stark challenge—balancing innovation with accountability in a sector worth $2.1tn globally.
The Future of Cybercrime: Predictions and Preparations
As Lazarus refines its tactics, analysts warn of an impending wave of AI-driven attacks. A 2025 report by cybersecurity firm CrowdStrike suggests North Korean hackers are experimenting with generative AI to craft hyper-realistic phishing emails, potentially bypassing current detection tools. Concurrently, advancements in quantum computing could render existing blockchain encryption obsolete within a decade, according to a MIT study published in January 2025.
On the defensive front, initiatives like the EU’s Digital Operational Resilience Act (DORA), effective from January 2025, mandate stress-testing for crypto firms’ cybersecurity frameworks. Meanwhile, insurers are adapting: Lloyd’s of London now offers policies covering crypto heists, albeit with premiums soaring by 300% since 2023. “The risk calculus is changing,” says Lloyd’s underwriter Eleanor Hartley. “Insurers demand proof of multi-layered security before offering coverage.”
Conclusion: A Global Imperative
The ByBit hack epitomises the escalating threat of state-sponsored cybercrime, blending technical sophistication with geopolitical audacity. With $3.6bn stolen by North Korean hackers since 2016—funding 60% of its missile tests, per South Korean intelligence—the stakes extend far beyond financial markets.
Combating this menace requires unprecedented collaboration. Governments must harmonise sanctions enforcement, while crypto firms prioritise transparency without stifling innovation. For users, vigilance is paramount: enabling two-factor authentication, verifying wallet addresses, and avoiding unsolicited job offers—a common Lazarus phishing tactic.
Ultimately, the Lazarus Group’s success hinges on systemic vulnerabilities. Closing these gaps demands not just better technology, but a reimagining of crypto’s social contract. As Dr Robinson starkly puts it: “Either the industry evolves, or it becomes a permanent ATM for rogue states.” The clock is ticking.
Recently Added
Categories
- Arts And Humanities
- Blog
- Business And Management
- Criminology
- Education
- Environment And Conservation
- Farming And Animal Care
- Geopolitics
- Lifestyle And Beauty
- Medicine And Science
- Mental Health
- Nutrition And Diet
- Religion And Spirituality
- Social Care And Health
- Sport And Fitness
- Technology
- Uncategorized
- Videos
